Home Our blog Windows 10 MDM Security Baseline - information and experience
Windows 10 MDM Security Baseline - information and experience
03/11/19
Pavel Otych
This summer, Microsoft has released the official Windows 10 MDM Security Baseline policies that make it easier to improve the security of Windows 10 client computers. The way to them was not easy, but let's take a look at what they bring.
What are security baselines
Windows security baselines is a group of settings that Microsoft recommends based on its experience from development teams, product groups, partners, and customers. The goal of these settings is to increase the security of Windows computers so that they meet standard security requirements. The specific settings are selected so thath users are prevented from changing certain features that could compromise system security, additionaly, settings that are unlikely to be intentionally changed by systems administrators are selected as wll. Baseline policies are also released for Defender ATP, Office and Edge (the one with the Chromium engine), but these are not to be discussed today.
History of Windows baseline policies
Looking back into the past, Microsoft has been heading for this product for a long time since 2010 when it released the Security Compliance Manager. It was able to download new baselines from Microsoft, analyze the set group policies and export the settings to SCCM DCM, SCAP and Excel. The tool was robust but too complex. It required to be updated for each version of Windows and, logically supported only group policies, not MDM policies. However, it was successfully used to configure Windows 7 and Internet Explorer.
However, since Windows 8/8.1, Microsoft releases baselines only in form of Excel spreadsheets, admx files, and to that adds the Microsoft Security Compliance Toolkit, which can compare recommended and set policies. This tool is still used to set up Windows 10 policies, but it should be reiterated that it can only manage group policies, not MDM settings.
To help migrate to device management via MDM, Microsoft released the MDM Migration Analysis Tool (MMAT) in 2017, which can compare group policies and let administrators know which settings can be managed via MDM and which are not. The stumbling block of MDM management is, of course, that while Windows has more than 3000 group policies, of which about 450 are set up in some way within the baseline, only about 150 can be set using MDM.
At Ignite 2018, Microsoft announced that there will be a simplified user interface in Intune called Windows 10 MDM Security Baseline to easily deploy baseline policies and discover whether devices comply with them. These are the above-mentioned roughly 150 settings from the original group policy-based baseline that can be set via MDM. Additionally, Microsoft adds a detailed description for each of them (a full list can be found here https://docs.microsoft.com/en-us/intune/protect/security-baseline-settings-mdm ) and removes some settings that aren't relevant to cloud management (editing domain/local accounts, etc.). This functionality was released by Microsoft in preview version in autumn 2018 and the final GA version was release in summer 2019.
Windows 10 MDM Security Baseline in Intune
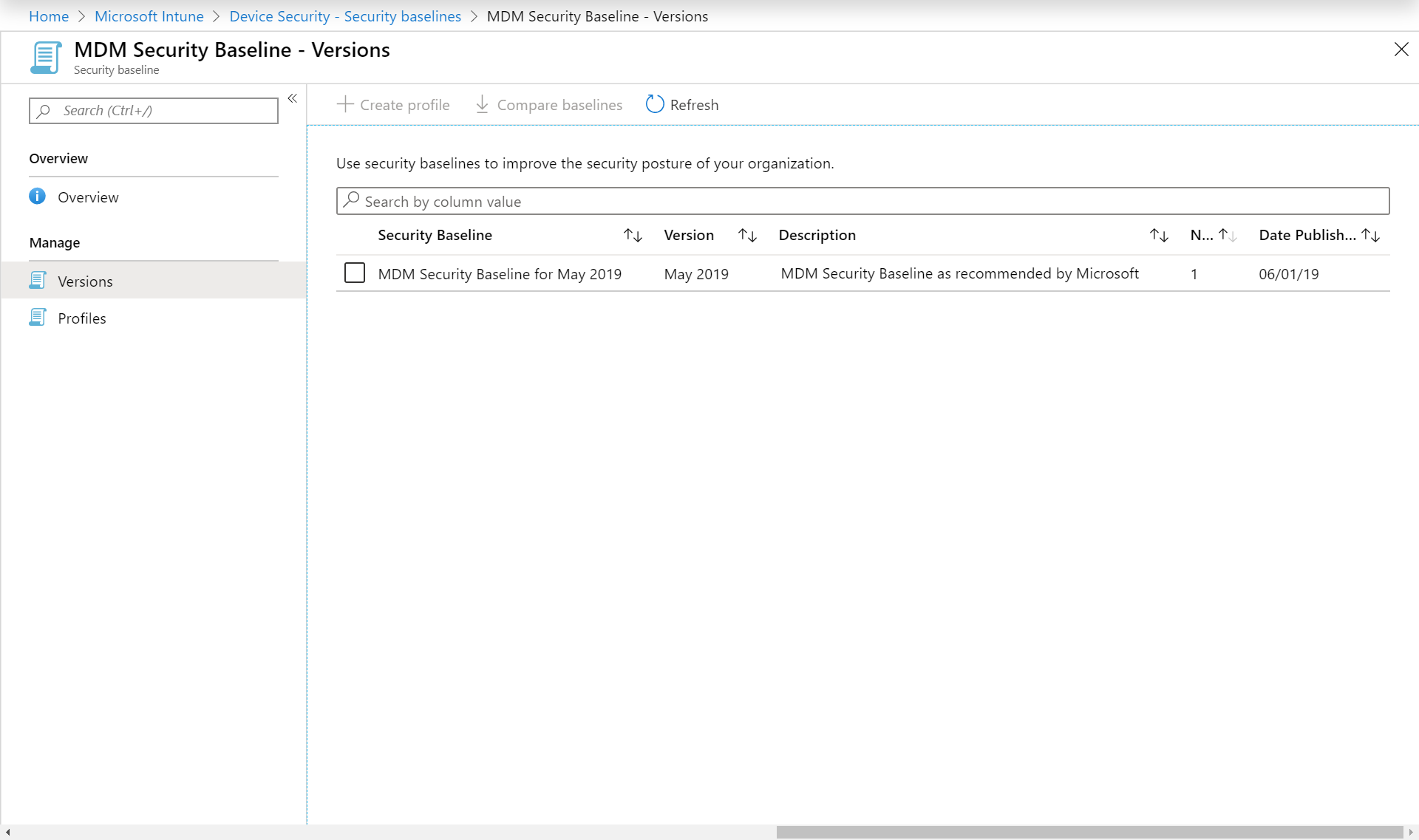
So now we have the option to apply baseline policies with just a few clicks. We can even compare baseline policies for different versions of Windows (e.g. 1809 vs 1903), so this is a promise that it will be relatively easy to see what the new Microsoft is changing in terms of recommendation and what new settings are being added.
The setup is simple, even though it is illogically hidden under Device Security in Intune - separate from other MDM settings. Anyway, we choose what baseline policy we want to set (currently only version 1903 is available, other versions will be added along with new versions of Windows) and then determine which devices will apply to, confirm a few times and we are done.
Simplicity is also a bit treacherous. At first glance, the administrator seems to have a pre-verified option, sets it up in a few clicks, the security of the Windows 10 device will suddenly increase to a Microsoft-defined level and everyone is happy. However, if you do not go through these 150 settings very carefully, you will be amazed at what your users will do differently or will stop working altogether.
What to watch out for when setting up Windows 10 MDM Security Baseline
Unfortunately, we do not have space to go through everything - as we said above, there are around 150 settings, but I would like to mention a couple that you should not ignore lightly and think about whether you really want to apply them.
BitLocker removable drive policy - write access
BitLocker encryption of all USB devices is required, which seems quite restrictive. There may be environments where this is desirable, but generally I think the vast majority of administrators will not want to turn this policy on. After all, every now and then everybody needs to copy a few files to USB. Data security can be solved in other ways.
Browser - Block Password Manager
It would seem that the policy blocks third-party password managers, but it also turns off standard password management in Microsoft Edge. This forces users to enter usernames and passwords wherever single sign on isn’t used, which in my opinion increases the risk - if the password is not saved in the browser and the user needs it often, he will write it on paper and hide it drawer. In the worst case, they stick the paper on the monitor.
Browser - Prevent certificate error overrides
I must admit that even our clients sometimes have internal servers without a trusted certificate installed. Most cases are infrequently used applications or network infrastructure devices that use self-signed certificates. It depends on the particular environment, but I would rather recommend to not use this setting.
Hardware device installation by device identifiers/setup classes
The default values block installation of all devices. If you have superbly managed devices and you know all devices that are being used in your company, it is great, and I envy you. But hand on heart, do users not need to install a network printer or USB device here and there? Remember that baseline policies are applied to the device, so when you come to the user and log on to his machine with a local administrator account, you still won't be able to install anything. Therefore, we recommend turning this policy off.
Exploit Guard
Exploit Guard technology replaces old EMET and has the same goal of reducing the ability to attack running processes by modifying some of their features (either enhancing protection or reducing what processes can do). Unfortunately, if you are not really an expert in Windows security and know exactly what processes you want to limit, we recommend not implementing this policy. In baseline settings, all Office processes are noticeably limited, so that even some add-ons developed by Microsoft (such as the Azure Information Protection add-on) do not work. We therefore recommend that you turn off this policy or thoroughly test it first.
Microsoft Defender - Office settings
Like above, some macro functions in Office are blocked in baseline settings (loading DLLs, running separate processes, etc.). Here we find the settings less problematic than Exploit Guard, but if you are using macros in Office, you need to thoroughly test whether you want to implement this policy.
Microsoft Defender Firewall - Inbound notifications blocked
This setting disables notifications that some applications have been blocked by Windows firewall. We recommend turning off the setting because it is more useful to get information "I cannot run application XYZ application, it is blocked by firewall", rather than " I cannot run application XYZ ".
Power - Standby states
The default setting blocks S1-S3 states, so devices do not go to sleep. This is useful if, for example, your devices require a PIN for BitLocker boot, but in practice it is quite unusual, so we recommend turning this policy off.
Remote Desktop Services - Block password saving and Block drive redirection
Like the Microsoft Edge policy above, which prohibits saving password, I believe that forcing users to retype RDP passwords does not automatically increase security. Block drive redirection also blocks copying and pasting into RDP sessions, which is quite a noticeable interference with user comfort. If you use Remote Apps or users often connect to a remote desktop, we recommend turning off this setting.
Disable indexing encrypted items
This setting determines whether the Windows Search Indexer can crawl encrypted data and display it to the user in search results. By default, this is disabled because Indexer separately stores unencrypted metadata. However, I think the risk of misuse of these metadata is minimal and if you use Windows Information Protection say goodbye to searching messages in Outlook. We therefore recommend that you turn this setting off.
Summary
From the above it is clear that easy setup of Windows 10 MDM Security Baseline can have quite a major impact on some Windows features and user comfort. We pointed out the most important settings above, but each company is individual, and it depends on your users what they need for their daily work and how you want to have your client computers secured.
