DEP becomes Automated Device Enrollment
The first important change is the renaming of the current Device Enrollment Program (DEP) to Automated Device Enrollment. If you buy corporate devices in bulk, so you will from now on be under this program. In most countries DEP devices can be purchase from official resellers or directly from Apple Stores, however, there are some countries in which DEP devices are available only from the official resellers.
You can also manually add devices purchased from a regular retail network to the Automated Device Enrollment but you need an Apple computer with Apple Configurator 2 to do so. It is still valid that such manually added devices remain in a trial period for 30 days and can be removed from the enterprise deployment in this timeframe. In practice, it would be problematic to assign such a device to a user for everyday use, so it is necessary to count with the fact that you cannot practically use the device for 30 days and it will lie on the table or somewhere in the warehouse.
An important change is that all devices registered in the Automated Device Enrollment are automatically enrolled in Supervised mode which offers a wider range of settings. This step is in line with Apple's current approach allowing many settings to apply only to company-owned devices that the IT department has full control of.
New way to enroll a device in iOS 13 - User Enrollment
Under pressure of circumstances, Apple is pushing for user data protection while somewhat inspired by Google and its Android Enterprise and its work profiles. In the latest version of iOS (no iPadOS yet but it's just a matter of time) Apple comes with a similar variant of device management and calls it User Enrollment. It is basically a lightweight device enrollment that protects user's personal data and is primarily intended for BYOD (Bring Your Own Device) scenarios.
Advantages of User Enrollment:
- Ideal for BYOD, when the user enters his / her device into the employer's IT department.
- The company data is stored on a separate APFS partition, the IT department cannot touch sensitive device information or employee's personal data.
- The user can access Apple services under both private and corporate Apple IDs
What is not so advantageous on User Enrollment:
- MDM policies for User Enrollment are significantly limited and the IT department does not have as much control over the device as with normal (Automated) Device Enrollment.
- Users to have a managed Apple ID that can only be federated with Azure AD (at least now and only in beta). This is probably a hard-to-overcome obstacle for all administrators who either do not use Azure AD or simply do not want to / cannot federate. It seems like Apple is pushing for the use of its services (iCloud, Pages, Numbers, Keynote, etc.) and decided that a possible solution is to for corporate users to have business managed Apple IDs. If you do not federate with Azure AD, you can manage your corporate Apple ID manually through Apple Business Manager, but in practice, this solution is only applicable to small companies or those who like to commit suicide or manually synchronize passwords to users in their free time.
- Devices cannot be wiped which is logically related to the limited management capabilities. This can be a problem when the device is lost or stolen, depending on other circumstances and how secure the device is.
What management options can we choose from
Apple has brough us a bit of confusion with the recent update, so let's summarize what MDM options we actually have to manage Apple devices:
- Automated Device Enrollment (original DEP) - absolute management of the device in which we can do with it what we want (= what Apple allows us). The device must be purchased in through DEP from an official distributor or Apple, the device is owned by the employer.
- Device Enrollment - management of device acquired in retail or by/from third parties. Usually used by from smaller companies or those who purchase through DEP.
- User Enrollment - enrollment suitable for BYOD scenarios, the user's private data is protected. However, a managed Apple ID is required.
- Mobile Aplication Management - Although it is not a device enrollment option (only applications are managed), it is a scenario that until now has been commonly used to protect company data on BYOD devices. We will see what the new User Enrollment possibilities will do about it but in any case, MAM is advantageous because it can be combined with the above device enrollment options. Therefore, we can manage the device and manage applications to streamline business data transfer between applications ( copy / paste / etc.).
User Enrollment in Intune
Currently, it is possible to enroll iOS devices via User Enrollment to Intune in preview version. There is nothing difficult in the setup - basically, we just need to create a new Enrollment type profile and we choose whether to enroll the device through Device Enrollment, User Enrollment, or leave the choice to users.
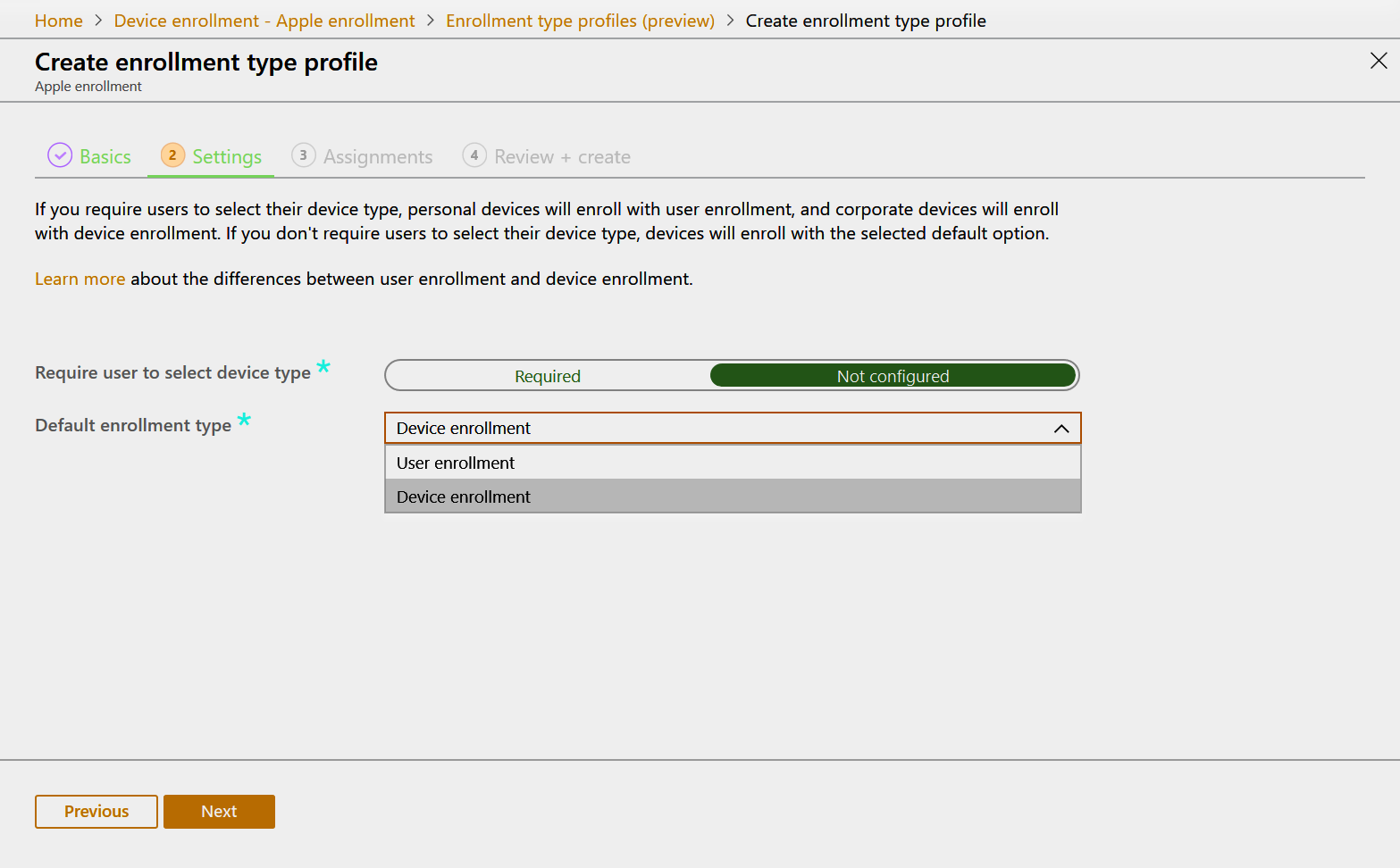
Of course, we can target Enrollment type profiles to different user groups. If there is no profile assigned, devices are enrolled in the old way, ie through Device Enrollment. Device enrollment from the user's point of view takes place through the Company Portal app, in both variants of enrollment Microsoft Authenticator app is installed on the device and it takes care authentication and conditional access requirements.
Summary
User Enrollment is a successful step of Apple in the direction of BYOD device enrollment. So far, however, the limitations are fundamental and too restrictive in practice (managed by Apple ID, limited federation in beta). It is a promise for the future rather than something we need to actively address or even re-register managed devices. In any case, it is expected that Apple's future steps in the BYOD management will lead in this direction and that is why it is appropriate to monitor developments in this area.
